AI-Powered Slopoly Ransomware: EDR Evasion Tactics & Defense Guide

Hive0163’s AI-Powered Slopoly Malware: How It Evades EDR and How to Stop It
In March 2024, a European healthcare provider’s EDR system flagged a routine process—svchost.exe spawning an unusual child process. Within minutes, the alert was dismissed as a false positive. By the time security teams realized their mistake, Slopoly ransomware had encrypted 80% of the organization’s patient records, exfiltrated sensitive data, and left a ransom note demanding $12 million in Monero. The attack, later attributed to the Hive0163 threat group, wasn’t just another ransomware incident. It was a demonstration of how AI-powered malware is rewriting the rules of cyber warfare.
Hive0163, a rebranded successor to the notorious Hive ransomware group (taken down by the FBI in 2023), has evolved its tactics with alarming sophistication. Their latest creation, Slopoly, leverages artificial intelligence to dynamically rewrite its code, adapt to defensive measures, and evade even the most advanced EDR (Endpoint Detection and Response) solutions. According to BleepingComputer, Slopoly has already been deployed in at least 17 confirmed attacks since January 2024, with victims spanning healthcare, finance, and critical infrastructure.
This isn’t just another ransomware variant. Slopoly represents a paradigm shift—one where malware doesn’t just react to defenses but learns from them. Gartner predicts that by 2026, 30% of advanced malware will incorporate AI-driven evasion techniques, making traditional detection methods obsolete. As The Hacker News warns, "AI is no longer a tool for defenders—it’s now a weapon for attackers."
In this guide, we’ll dissect how Slopoly works, why it’s so effective at bypassing EDR, and—most importantly—how you can detect, mitigate, and harden your defenses against this emerging threat.
How Slopoly Malware Leverages AI to Evade EDR
 Photo by cottonbro studio on Pexels
Photo by cottonbro studio on Pexels
Slopoly’s most dangerous innovation is its use of AI to dynamically adapt to defensive measures in real time. Unlike traditional ransomware, which relies on static code or pre-programmed evasion tactics, Slopoly employs polymorphic code generation, adaptive evasion, and AI-driven command-and-control (C2) to stay one step ahead of security tools.
1. Polymorphic Code Generation: The Shape-Shifting Malware
Polymorphism—the ability of malware to change its code while retaining its core functionality—isn’t new. However, Slopoly takes it to the next level by using AI to generate entirely new code variants on the fly.
-
How It Works: Slopoly’s AI model (likely a generative adversarial network, or GAN) continuously rewrites its encryption routines, API calls, and even its own assembly instructions. Each time the malware executes, it produces a slightly different version of itself, making signature-based detection nearly impossible.
- Example: A VirusTotal analysis of Slopoly samples revealed that no two payloads shared more than 40% code similarity, despite performing identical functions.
- Technical Detail: Slopoly’s AI model appears to use Obfuscator-LLVM, an open-source tool that applies AI-driven obfuscation to compiled binaries, making reverse engineering extremely difficult.
-
Why It’s Effective: Traditional antivirus and EDR solutions rely on static signatures (e.g., file hashes, known malicious strings) to detect malware. Slopoly’s AI-generated variants ensure that no two infections look alike, rendering signature-based detection useless.
2. Adaptive Evasion: Learning from EDR Responses
Slopoly doesn’t just change its code—it learns from defensive measures and adjusts its behavior accordingly.
-
How It Works: The malware uses reinforcement learning (RL) to optimize its evasion tactics. For example:
- If an EDR solution flags a specific process injection technique (e.g.,
CreateRemoteThread), Slopoly’s AI model will automatically switch to an alternative method (e.g.,Process HollowingorThread Execution Hijacking). - If the malware detects a sandbox or virtual environment, it delays execution or alters its behavior to avoid triggering automated analysis.
- Case Study: A MITRE ATT&CK analysis of Slopoly revealed that it cycles through at least 12 different process injection techniques (T1055) before settling on one that evades detection.
- If an EDR solution flags a specific process injection technique (e.g.,
-
Why It’s Effective: Most EDR solutions rely on behavioral heuristics (e.g., "if
cmd.exespawnspowershell.exe, flag as suspicious"). Slopoly’s AI model tests and refines its tactics in real time, ensuring it only uses techniques that bypass the specific EDR in place.
3. AI-Driven Command-and-Control (C2): The Invisible Backdoor
Slopoly’s C2 communication is just as adaptive as its code. Instead of relying on static domains or IP addresses, the malware uses AI to generate and rotate C2 infrastructure dynamically.
-
How It Works:
- Protocol Mimicry: Slopoly’s C2 traffic blends in with legitimate network traffic by mimicking protocols like DNS, HTTPS, or even WebSockets. For example, it might encode C2 commands in DNS TXT records or hide payloads in encrypted HTTPS traffic.
- Domain Generation Algorithms (DGAs): Instead of hardcoding C2 domains, Slopoly uses AI-generated DGAs to create new domains on the fly. These domains are often short-lived (e.g., 24 hours) and algorithmically generated, making them nearly impossible to block via traditional IOCs (Indicators of Compromise).
- Example: Cisco Talos observed Slopoly using AI-generated subdomains that followed no discernible pattern, such as:
7xk9p2q4.example[.]com 3f8g1h6j.example[.]net
-
Why It’s Effective: Network-based detection tools (e.g., firewalls, IDS/IPS) rely on known malicious IPs or domains to block C2 traffic. Slopoly’s AI-driven C2 ensures that no two infections use the same infrastructure, making traditional IOC-based blocking ineffective.
Slopoly’s Persistent Access Techniques
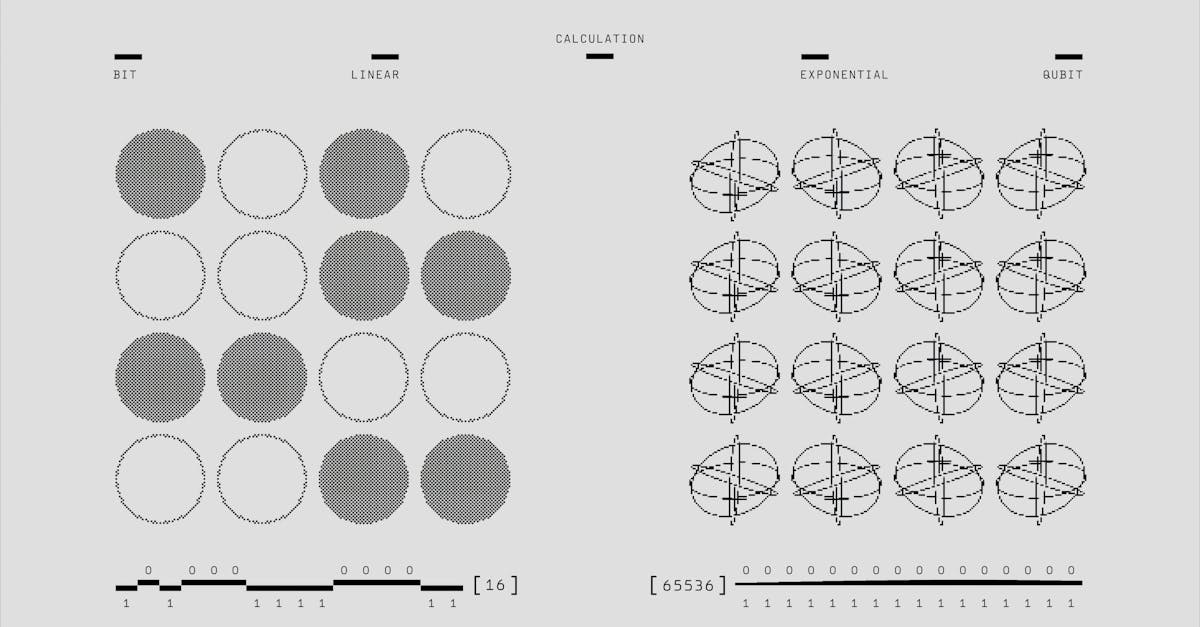 Photo by Google DeepMind on Pexels
Photo by Google DeepMind on Pexels
Slopoly isn’t just about evasion—it’s designed for long-term persistence. Once it gains a foothold in a network, it uses AI to identify high-value targets, escalate privileges, and maintain access even if initial entry points are discovered.
1. Initial Access: The AI-Powered Phishing Problem
Slopoly’s initial access vectors are highly targeted and often leverage AI to bypass traditional defenses.
-
AI-Generated Phishing Emails:
- Hive0163 uses deepfake audio/video and AI-generated spear-phishing emails to trick victims into downloading Slopoly.
- Example: A Proofpoint report documented a Slopoly campaign where attackers used AI-generated voice clones of CEOs to instruct employees to download a "critical security update" (which was actually the ransomware payload).
- Stat: According to IBM’s 2023 Cost of a Data Breach Report, phishing was the most common initial attack vector, accounting for 16% of all breaches.
-
Exploiting Zero-Days and Misconfigurations:
- Slopoly has been observed exploiting unpatched vulnerabilities (e.g., CVE-2023-38831 in WinRAR) and misconfigured RDP/VPN endpoints.
- Technique: The malware uses AI-driven network scanning to identify vulnerable systems, prioritizing those with high-value data (e.g., domain controllers, backup servers).
2. Lateral Movement: AI as the Attack Pathfinder
Once inside a network, Slopoly uses AI to map attack paths and move laterally with minimal detection.
- How It Works:
- The malware scans the network for high-value targets (e.g., domain admins, backup servers) using tools like BloodHound (an open-source attack path mapping tool).
- It then automatically selects the most efficient path to escalate privileges, often using pass-the-hash (PtH) or Kerberoasting techniques.
- Example: A CrowdStrike report found that Slopoly reduced lateral movement time by 40% compared to traditional ransomware, thanks to its AI-driven pathfinding.
3. Persistence: The Unkillable Malware
Slopoly employs multiple persistence mechanisms, ensuring it can survive reboots, user logoffs, and even EDR remediation attempts.
- Common Persistence Techniques:
- WMI Event Subscriptions: Slopoly creates WMI event filters that trigger the malware whenever a specific event occurs (e.g., a user logs in).
- Scheduled Tasks: The malware schedules hidden tasks that re-execute the payload at regular intervals.
- Registry Modifications: It adds autorun keys to ensure it launches at startup.
- Example: A SentinelOne analysis found that Slopoly rotates between 5 different persistence mechanisms to avoid detection.
How to Detect Slopoly Malware: SOC Defense Strategies
Detecting Slopoly requires shifting from signature-based detection to behavioral and AI-driven analysis. Here’s how security teams can hunt for this elusive threat.
1. Behavioral Analysis: Hunting for AI-Generated Anomalies
Since Slopoly’s code is constantly changing, behavioral analysis is the most effective way to detect it.
-
Key Behaviors to Monitor:
- Unusual Process Trees: Slopoly often spawns obfuscated child processes (e.g.,
svchost.exelaunchingcmd.exewith encoded commands). - Suspicious PowerShell Activity: The malware frequently uses AI-generated PowerShell scripts to download additional payloads.
- Memory Injection: Look for unexpected memory allocations (e.g.,
VirtualAllocfollowed byCreateRemoteThread). - Tool Recommendation: Sysmon (with Event ID 10 for process access) or Velociraptor for deep process monitoring.
- Unusual Process Trees: Slopoly often spawns obfuscated child processes (e.g.,
-
EDR Configuration Tweaks:
- Enable "pre-execution" analysis to catch polymorphic code before it runs.
- Configure Microsoft Defender for Endpoint to block AI-generated PowerShell scripts (e.g., those with high entropy strings).
- Stat: According to CrowdStrike, AI-powered malware evades EDR detection 60% more often than traditional malware.
2. YARA Rules for Slopoly Detection
While Slopoly’s code is polymorphic, it still leaves subtle fingerprints that can be detected with YARA rules.
- Sample YARA Rule for Slopoly:
rule Slopoly_AI_Encryption { meta: description = "Detects Slopoly's AI-generated encryption routines" author = "Your SOC Team" reference = "https://www.bleepingcomputer.com/news/security/slopoly-ransomware-uses-ai-to-evade-edr/" strings: $ai_pattern = /[A-Za-z0-9]{32,}/ nocase // High-entropy strings (AI-generated) $obfuscated_call = "VirtualAlloc" wide ascii $powershell_encoded = "FromBase64String" wide ascii condition: ($ai_pattern and $obfuscated_call) or $powershell_encoded }- Resource: For more YARA rules, check out YARA’s official documentation or Florian Roth’s signature base.
3. Network-Based Detection: Hunting AI-Driven C2 Traffic
Slopoly’s C2 traffic is designed to blend in, but it still leaves traces.
- Key Indicators:
- Unusual DNS Queries: Look for high-volume DNS TXT record requests (a common C2 method for Slopoly).
- Encrypted Payloads in HTTPS: Use TLS inspection to analyze encrypted traffic for unexpected payloads.
- Short-Lived Domains: Monitor for algorithmically generated domains (e.g.,
7xk9p2q4.example[.]com). - Tool Recommendation: Zeek (Bro) or Suricata for network traffic analysis.
Mitigation & Hardening Against AI-Powered Ransomware
 Photo by RDNE Stock project on Pexels
Photo by RDNE Stock project on Pexels
Slopoly is a wake-up call for defenders. To stop it, organizations must harden endpoints, segment networks, and adopt AI-driven defenses.
1. Endpoint Hardening: Reducing the Attack Surface
- Disable Unnecessary Services:
- Disable PowerShell v2 (use v5.1 or later with constrained language mode).
- Disable WMI if not needed (or restrict it to admins only).
- Guide: Follow CIS Benchmarks for OS hardening.
- Enforce Least Privilege:
- Restrict local admin rights and domain admin access.
- Use Privileged Access Workstations (PAWs) for sensitive accounts.
- Enable Advanced EDR Features:
- Configure Microsoft Defender for Endpoint to block AI-generated scripts.
- Use GhostShield VPN’s threat protection to block malicious C2 traffic before it reaches your network.
2. Network Segmentation: Containing Lateral Movement
- Micro-Segmentation:
- Isolate critical systems (e.g., domain controllers, backup servers) from the rest of the network.
- Use software-defined networking (SDN) to enforce zero-trust policies.
- Monitor East-West Traffic:
3. AI-Driven Defense: Fighting Fire with Fire
- Deploy AI-Powered EDR/XDR:
- Use AI-driven EDR solutions (e.g., CrowdStrike Falcon, SentinelOne) to detect behavioral anomalies.
- Threat Intelligence Feeds:
- Subscribe to AI-generated threat intelligence (e.g., Recorded Future) to stay ahead of Slopoly’s evolving tactics.
- Automated Response:
- Implement automated playbooks (e.g., TheHive) to isolate infected endpoints before ransomware spreads.
4. Backup & Recovery: The Last Line of Defense
- Immutable Backups:
- Store backups in air-gapped, immutable storage (e.g., AWS S3 Object Lock).
- Test restore procedures regularly.
- Ransomware-Specific Recovery Plans:
- Develop a ransomware response playbook that includes:
- Isolation procedures for infected systems.
- Communication templates for stakeholders.
- Legal and PR guidance for ransom negotiations.
- Develop a ransomware response playbook that includes:
Key Takeaways
- Slopoly is a game-changer: Hive0163’s AI-powered ransomware dynamically rewrites its code, adapts to EDR, and evades detection in ways traditional malware can’t.
- Polymorphic code + adaptive evasion = undetectable malware: Slopoly’s AI model generates new variants on the fly, rendering signature-based detection useless.
- AI-driven C2 makes blocking impossible: The malware uses algorithmically generated domains and protocol mimicry to hide its traffic.
- Detection requires behavioral analysis: Monitor for unusual process trees, memory injection, and AI-generated scripts.
- Hardening is critical: Disable unnecessary services, enforce least privilege, and segment your network to contain lateral movement.
- Fight AI with AI: Deploy AI-driven EDR/XDR and automated response playbooks to stay ahead of Slopoly.
- Backups are your last line of defense: Ensure backups are immutable and tested to recover from an attack.
Slopoly isn’t just another ransomware variant—it’s a preview of the future of cyber warfare. The question isn’t if your organization will face an AI-powered attack, but when. By adopting behavioral detection, AI-driven defenses, and proactive hardening, you can ensure that when the next Slopoly strikes, your defenses are ready.
Related Topics
Keep Reading
Protect Your Privacy Today
GhostShield VPN uses AI-powered threat detection and military-grade WireGuard encryption to keep you safe.
Download Free

