How to Secure Your Browser from Malicious Chrome Extension Attacks

The Silent Threat: How "Legit" Extensions Turn Malicious
You installed that handy toolbar or productivity booster from the official Chrome Web Store. It passed Google's automated checks, has thousands of five-star reviews, and has worked flawlessly for months. It is, by all appearances, trustworthy. This is precisely what makes the next stage of the attack so effective.
The primary vector for this threat isn't a shady download from a random website; it's a fundamental flaw in the extension ecosystem's business model: ownership transfer. The lifecycle is alarmingly common. An independent developer builds a useful, popular extension. As its user base grows into the hundreds of thousands, it becomes a valuable asset. The developer receives an offer to sell, often from a seemingly legitimate entity. Once the transfer is complete, the new owner pushes an "update." This update, now signed with the same official credentials and delivered through the trusted marketplace, can quietly replace the benign code with malicious payloads. The Hacker News report from late 2023 detailed numerous cases of this exact scenario, where extensions with over 100,000 active users began injecting advertisements, cryptocurrency mining scripts (cryptojacking), and data-harvesting code.
Once compromised, these extensions wield significant power through the permissions you've already granted them. The attack methods are severe:
- Code Injection: An extension with permission to "read and change all your data on the websites you visit" can silently modify any page you load. The most dangerous application is on banking or e-commerce checkout pages, where it can inject credit card skimming code, a technique historically associated with "Magecart" attacks but now enabled from within your browser.
- Data Theft: Permissions to "access your data for all websites" or "read your browsing history" become tools for comprehensive surveillance. The extension can exfiltrate your complete browsing history, saved passwords, authentication cookies (which could allow session hijacking), and even capture keystrokes.
- Bypassing Defenses: This is the critical nuance. Because the malicious code runs at the browser's privileged extension level, it operates after network traffic is decrypted (e.g., from an HTTPS website). This means traditional network firewalls and many endpoint antivirus solutions see only legitimate, encrypted traffic to and from your browser, not the malicious activity happening inside it. The extension has effectively bypassed your primary security layers.
Step 1: The Extension Audit & Purge
 Photo by Fernando Hernandez on Unsplash
Photo by Fernando Hernandez on Unsplash
Your first and most powerful action is a ruthless inventory. Every installed extension is a potential attack surface, regardless of its source. The goal is to minimize this surface area.
Conduct a Rigorous Inventory Navigate to your browser's extension management page:
- Chrome/Edge: Type
chrome://extensionsoredge://extensionsinto the address bar. - Firefox: Type
about:addonsand click "Extensions."
You will see a list of every installed extension. Apply a simple, strict rule: If you haven't actively used it in the last two weeks, remove it. Be honest with yourself. That coupon finder, weather widget, or niche toolbar you used once six months ago must go. Click "Remove."
Evaluate Every Permission For the extensions that survive the initial purge, you must scrutinize their permissions. Click "Details" on each one. Pay acute attention to permissions like:
- "Read and change all your data on the websites you visit"
- "Access your data for all websites"
- "Read your browsing history"
A 2023 academic study by the CISPA Helmholtz Center for Information Security found that over 70% of Chrome extensions request what they classify as "potentially dangerous" permissions. The key question you must ask for each permission is: "Is this broad access absolutely necessary for the extension's core functionality?"
A password manager needs access to all sites to auto-fill. A dark mode extension needs to modify page styles. Does a PDF viewer or a grammar checker need to "read and change all your data"? Almost certainly not. If the permissions seem excessive for the stated purpose, remove the extension and search for a more privacy-conscious alternative.
Step 2: Locking Down Your Browser's Security Settings
Your browser has built-in security tiers; you need to enable the strongest ones.
Configure Built-in Browser Defenses
- Chrome/Edge: Go to
Settings > Privacy and security > Security. Select "Enhanced protection" mode. This enables proactive phishing and malware detection, predicts dangerous events, and sends URLs to Google Safe Browsing for real-time analysis. It significantly raises the bar. Furthermore, ensure "Developer mode" in yourchrome://extensionspage is toggled OFF unless you are actively developing an extension. - Firefox: Firefox takes a more restrictive stance by default. Go to
about:addonsand under the settings cog, you can set "Allow extensions to run in Private Windows" to "Ask to Activate" for an extra layer of control. Harden your general privacy settings viaabout:preferences#privacyby selecting "Strict" tracking protection.
Implement Network-Level Protection Since malicious extensions often need to communicate with command-and-control servers to exfiltrate data or receive instructions, blocking these requests at the network level is a highly effective secondary defense.
- Use a DNS filtering service like NextDNS, Control D, or a self-hosted AdGuard Home. These services can block requests to known malicious, advertising, and tracking domains, effectively neutering a compromised extension's ability to "phone home."
- For Chrome/Edge users, you can enable an experimental flag to block insecure requests. Type
chrome://flags/#block-insecure-private-network-requestsand set it to "Enabled." This helps prevent certain types of local network attacks that could be facilitated by an extension.
Step 3: Proactive Monitoring & Behavioral Red Flags
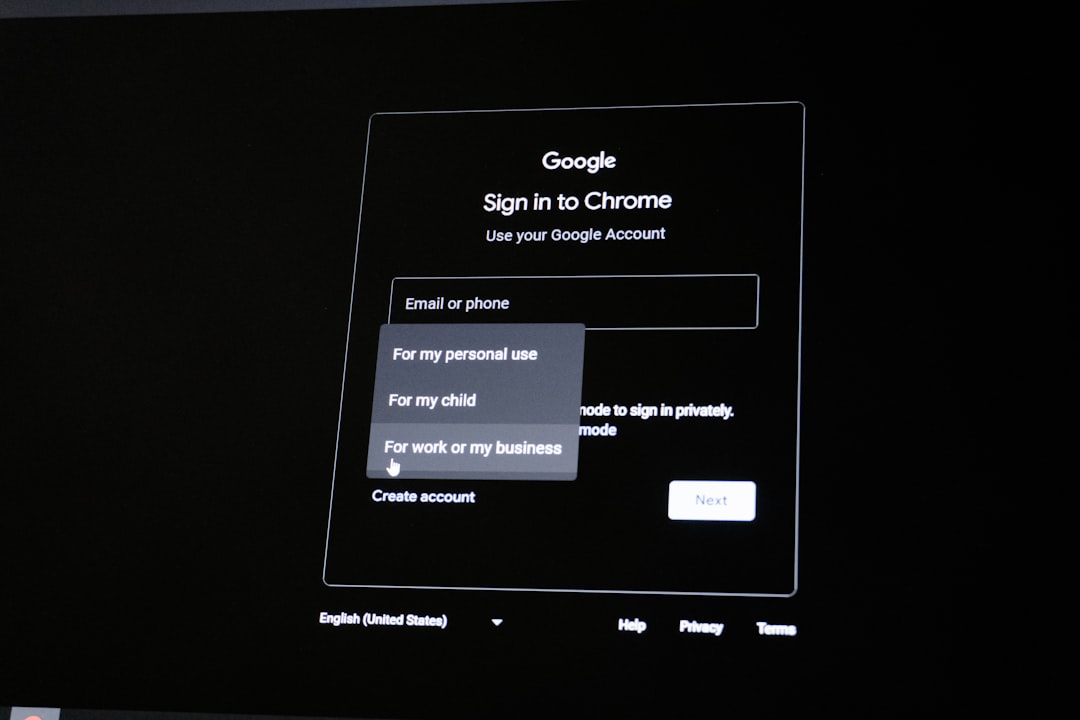 Photo by Zulfugar Karimov on Unsplash
Photo by Zulfugar Karimov on Unsplash
Security is not a one-time audit; it's an ongoing process. You need to monitor the behavior of the extensions you've chosen to keep.
Tools for Ongoing Vigilance
- Extension Watchdogs: Use tools designed for transparency. CRX Viewer (available as a web app) allows you to inspect the source code of any extension by entering its Chrome Web Store ID. Look for obfuscated, minified code or calls to unfamiliar external domains. Extensions Monitor (a Chrome extension itself) can track permission changes over time, alerting you if a trusted extension suddenly requests new, broader access.
- Browser Native Tools: Your browser has a built-in task manager. In Chrome or Edge, press Shift+Esc. This window shows every tab, extension, and plugin running, along with its current CPU and memory usage. A previously lightweight extension that suddenly shows consistently high resource consumption could be a red flag for cryptojacking or intensive data processing.
Red Flags That Demand Immediate Action If you observe any of the following, uninstall the extension immediately:
- Frequent, Vague Updates: The extension updates often with changelogs that only state "bug fixes" or "performance improvements" without specific details.
- New Browser Anomalies: You begin seeing unexpected advertisements, pop-ups, or redirects on websites that were previously clean. Your browser may feel sluggish.
- Permission Creep: Upon an update, the browser prompts you that the extension now requires new permissions. This is a major warning sign.
- Changed Ownership: If you read news or reviews indicating the extension has been sold to a new developer or company, treat it with extreme suspicion and consider preemptively finding an alternative.
Advanced Measures for High-Risk Users & Admins
For IT administrators, security professionals, or individuals handling highly sensitive data, more stringent controls are necessary.
For Organizations (Chrome/Edge) Enterprise management is the gold standard. Using Group Policy on Windows or administrative templates for Chrome/Edge, administrators can enforce a strict allowlist.
- The
ExtensionInstallAllowlistpolicy lets you specify only the official extension IDs that users are permitted to install. - The
ExtensionInstallBlocklistpolicy can block known malicious or unwanted extensions. - The
ExtensionSettingspolicy offers granular control, including automatically installing certain extensions and blocking all others. This creates a locked-down environment where users cannot install potentially dangerous add-ons.
Consider Alternative Architectures Segregation of duties is a core security principle. Apply it to your browsing:
- Use Separate Browser Profiles: Create one "clean" browser profile with zero extensions installed for sensitive activities: online banking, investment accounts, primary email, and corporate single-sign-on portals. Use a separate profile with your daily driver extensions for general browsing, work, and entertainment. This physically isolates your high-value sessions from the extension attack surface.
- Virtual Machine for Ultra-High-Risk Tasks: For activities like accessing a new financial service or testing unknown software, use a disposable virtual machine (using VirtualBox or VMware). Once the task is complete, revert the VM to a clean snapshot. This provides absolute isolation from your host machine.
A final, foundational layer for any high-risk activity is ensuring your connection itself is private and encrypted. While a VPN like GhostShield cannot stop a malicious extension from acting on data already inside your browser, it secures the pipeline to and from your device, preventing ISP snooping or man-in-the-middle attacks on public Wi-Fi that could compound a breach. GhostShield's use of the modern WireGuard protocol ensures this protection is both robust and high-performance.
Key Takeaways
- Ruthless Audit is Job One: Your extension list is your attack surface. Regularly review and remove anything non-essential. Scrutinize every permission critically.
- Ownership Changes are a Major Risk: Be deeply skeptical of extensions that have been sold to new developers. This is the primary method for turning trusted tools into attack vectors.
- Leverage Built-in Browser Hardening: Do not use the "Standard" security setting. Enable "Enhanced protection" in Chrome/Edge or "Strict" tracking in Firefox.
- Monitor for Anomalies: Unexpected browser behavior, performance degradation, and new permission requests are not glitches—they are primary indicators of a compromised extension.
- No Extension is Inherently Trustworthy: Adopt a zero-trust mindset. An extension's security can be invalidated by a single malicious update pushed through the official store.
The browser extension ecosystem delivers incredible functionality but operates on a fragile model of trust. Security in this context isn't about finding a perfectly safe extension—it doesn't exist. It's about proactively managing risk through disciplined habits: minimizing your exposure, configuring your defenses, and maintaining vigilant oversight. The most effective action you can take is the simplest. Open your browser's extension page now and start your audit. Your next ten minutes could prevent your next major security incident.
Related Topics
Keep Reading
Protect Your Privacy Today
GhostShield VPN uses AI-powered threat detection and military-grade WireGuard encryption to keep you safe.
Download Free
